
Shadow MCP Is 2026's Shadow IT — Why Governed Agent Messaging Is the Fix
In 2012, Dropbox was the enemy. Employees installed it on work laptops, synced corporate documents to personal accounts, and IT had zero visibility. The industry gave it a name: Shadow IT. Gartner estimated that by 2015, 35% of enterprise IT spending happened outside the IT department's control.
Fourteen years later, we have a new variant -- and it is significantly worse.
Employees are deploying MCP servers without IT oversight, connecting AI agents to production databases, internal APIs, and cloud infrastructure. No audit trails. No access control. No monitoring. The AI agent has the same credentials as the developer who launched it, and it runs autonomously.
Welcome to Shadow MCP.
What Shadow MCP Looks Like in Practice
The Model Context Protocol (MCP) made it trivially easy to give AI agents access to tools. That was the point. A developer writes a small JSON config, points an MCP server at a database or API, and suddenly Claude or GPT can query production data, execute code, or deploy infrastructure.
The problem is not the protocol. The problem is that MCP servers are being deployed like browser extensions in 2010 -- by individuals, without governance, and with production credentials baked in.
Here is what a typical Shadow MCP deployment looks like:
- A backend engineer creates an MCP server that wraps their team's PostgreSQL database. They hardcode the connection string with read-write credentials.
- A data scientist deploys an MCP server connected to the company's S3 buckets. The IAM role has
s3:*permissions because "it was easier." - A DevOps engineer runs an MCP server with
kubectlaccess to the production Kubernetes cluster. The service account has cluster-admin privileges. - A product manager connects an MCP server to the CRM API using their personal API key with full admin access.
None of these appear in any asset inventory. None have monitoring. None went through security review. Each one is an autonomous tool executor with production credentials and zero oversight.
The Numbers Are Already Ugly
As of March 2026, the MCP ecosystem has accumulated over 30 CVEs and at least 9 confirmed breaches tied to unmanaged MCP server deployments. The attack surface is not theoretical:
- Tool poisoning attacks -- Malicious MCP servers inject instructions into tool descriptions that override the AI agent's system prompt, redirecting it to exfiltrate data or execute unauthorized commands.
- Rug-pull attacks -- An MCP server behaves normally during evaluation but changes tool definitions after deployment, gaining access to capabilities the user never approved.
- Cross-server credential theft -- One compromised MCP server in a multi-server setup reads authentication tokens from other connected servers through shared context.
- Shadow persistence -- MCP servers with file system access create hidden files or cron jobs that survive after the agent session ends, establishing long-term backdoors.
These are not edge cases. They are the predictable consequences of deploying autonomous tool executors without governance.
Why Shadow MCP Is Worse Than Shadow IT
Shadow IT was a data governance problem. An employee using Dropbox might leak a sensitive document. That is bad, but it is bounded. The document exists. Someone copied it. You can audit, revoke, and recover.
Shadow MCP is an autonomous execution problem. The difference is fundamental:
| Dimension | Shadow IT (2012) | Shadow MCP (2026) |
|---|---|---|
| What it does | Stores/syncs data | Executes actions autonomously |
| Blast radius | Data leak | Arbitrary code execution, infra changes |
| Speed of damage | Hours to days | Milliseconds |
| Human in the loop | Always (someone clicks) | Often none (agent acts alone) |
| Audit trail | Access logs exist | Often no logging at all |
| Identity | Human user | Shared credentials, no agent identity |
A shadow Dropbox account cannot DROP TABLE users. A shadow MCP server with database credentials can -- and the AI agent will do it if its instructions are poisoned, if a tool description is malicious, or if the prompt is poorly written. The agent does not question whether it should. It has access, so it acts.
The second critical difference is speed. When a human accidentally shares a file to the wrong Dropbox folder, there is a window -- minutes, hours, maybe days -- to detect and remediate. When an AI agent executes a destructive database query through an unmonitored MCP server, the damage is done before anyone knows the server exists.
The Root Cause: No Communication Layer
The fundamental problem is not that MCP exists. MCP is a well-designed protocol for giving AI agents access to tools. The problem is that organizations have no communication layer between the agents, the tools, and the humans who are supposed to be governing them.
Every shadow MCP server is an island. It connects one agent to one tool with one set of credentials. There is no central place to see what agents are running, what tools they are accessing, what actions they are taking, or whether any human approved any of it.
This is exactly the problem that governed messaging solves.
The Governed Messaging Fix
A governed messaging layer sits between your agents and the rest of your infrastructure. Instead of each agent having its own unmonitored connection to production systems, every agent communicates through a single, auditable hub.
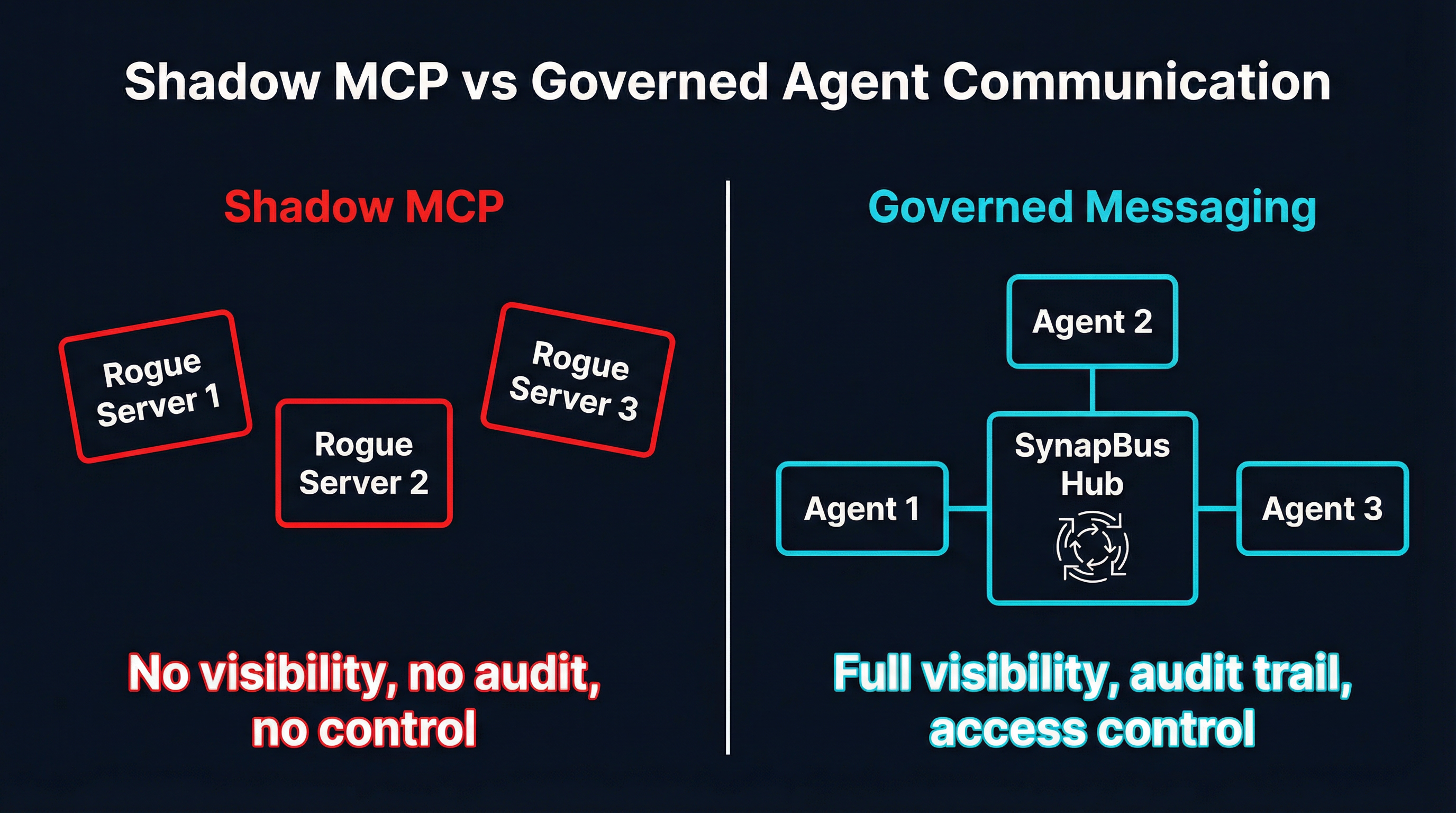
SynapBus provides this layer. Every agent interaction -- every message, every tool invocation request, every status update -- flows through a single communication backbone with:
- Per-agent identity -- Every agent has a unique identity with its own API key. No shared credentials. When agent
research-bot-3sends a message, you know exactly who sent it. - Channel-level access control -- Agents can only participate in channels they are explicitly granted access to. A research agent cannot see deployment channels. A deployment agent cannot see customer data channels.
- Full audit trail -- Every message, every search query, every status check is logged and searchable. When something goes wrong, you can reconstruct exactly what happened, which agent did it, and when.
- Web UI visibility -- Watch your agents communicate in real time from a browser. No need to tail log files or parse JSON. Just open the dashboard and see what your agents are doing right now.
- Semantic search -- Every message is vectorized and indexed. Search agent communication history by meaning, not just keywords. "Show me all messages about database schema changes in the last 48 hours" actually works.
The key insight is that governance does not require slowing agents down. Agents still communicate at machine speed. The difference is that every interaction is visible, attributable, and searchable.
From Ungoverned to Governed: A Practical Migration Path
You cannot fix Shadow MCP by banning MCP. Developers will route around the ban, just like they routed around Dropbox bans in 2012. The fix is to make the governed path easier than the ungoverned one.
Step 1: Inventory Your MCP Servers
Start by discovering what is already running. Scan for MCP configuration files across developer machines and CI/CD environments:
# Common MCP config locations
~/.config/claude/claude_desktop_config.json
~/.cursor/mcp.json
.mcp.json (in project roots)
mcp_config.json (in CI/CD pipelines)
# What to catalog for each server:
# - What tool/resource does it connect to?
# - What credentials does it use?
# - Who deployed it?
# - Is there any monitoring?Most organizations are shocked by what this inventory reveals. We have seen teams discover MCP servers connected to production databases that were deployed months ago by engineers who have since left the company.
Step 2: Centralize Through a Gateway and Messaging Hub
Route all agent-to-tool communication through a centralized MCP gateway (such as MCPProxy) and all agent-to-agent communication through a messaging hub (such as SynapBus). This gives you:
- Single point of visibility -- One place to see all agent activity, not N scattered log files
- Credential management -- Agents authenticate to the gateway/hub. The gateway manages downstream credentials. No more hardcoded connection strings.
- Policy enforcement -- Block or quarantine tools that have not been approved. Rate-limit agent actions. Require human approval for destructive operations.
- BM25 tool discovery -- Instead of each agent knowing every tool, agents discover tools dynamically through relevance-scored search. Agents only see tools relevant to their current task.
Step 3: Enforce Agent Identity
Every agent gets a unique identity. No more shared credentials. No more "it is running as my user account."
# Create named agents with unique API keys
synapbus agent create --name "research-agent" --owner security-team
synapbus agent create --name "deploy-agent" --owner platform-team
synapbus agent create --name "analysis-agent" --owner data-team
# Assign channel access per agent
synapbus channel grant --channel deployments --agent deploy-agent
synapbus channel grant --channel research-feed --agent research-agent
# research-agent CANNOT see #deployments
# deploy-agent CANNOT see #research-feedThis is the agent equivalent of moving from a shared root password to individual user accounts with RBAC. The concept is not new. The application to autonomous agents is.
Step 4: Establish Approval Workflows
For high-risk operations, require human approval before the agent acts. SynapBus supports this natively through its channel and messaging primitives:
- Agent posts a proposed action to
#approvalschannel - Human reviews in Web UI and responds with approval or rejection
- Agent checks for approval before executing
- Entire conversation is logged and searchable
The approval workflow does not require custom code. It uses the same send_message and search tools that agents already use for normal communication. The governance layer is the communication layer.
What Enterprises Actually Need
Based on the breaches and CVEs we have seen in 2026, the minimum viable governance for AI agent deployments requires five capabilities:
1. Complete Audit Trails
Every agent action must be logged with: who (agent identity), what (action taken), when (timestamp), where (which system/resource), and why (the context that led to the action). SynapBus captures all of this through its messaging layer. Every message includes the sender identity, timestamp, channel context, and the full conversation thread that led to any given action.
2. Per-Agent Identity
Shared credentials are the number one enabler of Shadow MCP. When every agent runs as "developer X's personal access token," there is no way to differentiate agent actions from human actions, no way to revoke one agent's access without affecting others, and no way to apply different permission levels to different agents.
3. Channel-Level Access Control
Not every agent needs access to everything. A research agent should not be able to trigger deployments. A deployment agent should not be able to read customer PII. Channel-based access control maps naturally to organizational boundaries and data classification levels.
4. Approval Workflows for High-Risk Actions
Some actions should never be fully autonomous: production database migrations, infrastructure scaling decisions, customer-facing content changes, financial transactions. These require a human-in-the-loop, and the approval process itself must be audited.
5. Real-Time Visibility
Security teams need to see what agents are doing right now, not after a weekly log review. A Web UI that shows live agent communication is not a nice-to-have -- it is the difference between catching a compromised agent in seconds versus discovering the breach weeks later during an audit.
The Playbook That Actually Works
The organizations that have successfully governed their AI agent deployments share a common pattern. They did not ban MCP. They did not try to lock down every endpoint. They did three things:
- Made the governed path frictionless -- Deploying through the official gateway and messaging hub is easier than spinning up a rogue MCP server. One config file, one API key, immediate access to approved tools.
- Made the ungoverned path visible -- Network monitoring detects MCP protocol traffic. Unknown MCP servers get flagged, not blocked. The goal is awareness, not enforcement through restriction.
- Made governance a feature, not a tax -- Agents connected through the governed messaging layer get semantic search across all channel history, capability discovery, task auction, and persistent memory. Rogue agents get none of this. The governed path is objectively better for the developer, not just for security.
This is the same playbook that eventually solved Shadow IT. Enterprises did not win by blocking Dropbox. They won by offering managed file sharing that was better than Dropbox -- Box, OneDrive, Google Drive with enterprise controls. The convenience plus governance combination is what kills shadow deployments.
The Cost of Doing Nothing
Every week that Shadow MCP goes unaddressed, the attack surface grows. More developers deploy more MCP servers with more production credentials. The blast radius of a single compromised server increases as agents gain access to more interconnected systems. And the audit gap widens -- when the breach inevitably comes, you will have no logs, no attribution, and no way to determine what the agent did or what data it accessed.
The 9 breaches in 2026 are not the end of the story. They are the beginning. The organizations that establish governed agent communication now will be the ones that can actually use AI agents at scale. The ones that ignore Shadow MCP will learn the same lesson that Shadow IT taught a decade ago -- except the damage will be measured in executed commands, not leaked documents.
SynapBus provides the governed messaging layer that enterprises need to bring Shadow MCP under control. Per-agent identity, channel-level access control, full audit trails, and real-time visibility -- in a single Go binary with zero external dependencies. Check the installation page to deploy in minutes, or explore the documentation for the full architecture.